If the “office” is defined by devices then “workplace” is defined by the ability to work from wherever those devices (and their users) are located. In this vein, “work” typically includes a requirement to access corporate data with mobile devices.
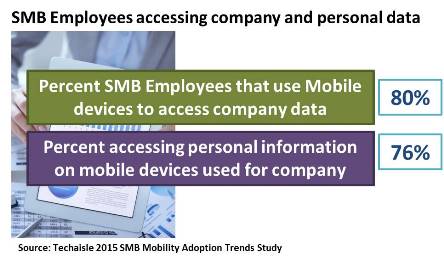
Data from the Techaisle 2015 SMB Mobility Adoption and Trends survey finds that more than 80% of small business employees and 55% of workers in midmarket firms require mobile access to company data. Providing this access and the applications, devices and solutions represents an enormous investment for SMBs that are typically very conservative in their IT budget allocations.
By more than a 2:1 ratio, SMB respondents believe that mobility is a means of driving growth in the business. But mobility does not deliver business benefits painlessly. The introduction of mobility solutions has created new issues for IT management, and suppliers who can help to address these issues will gain favor in this community.
Addressing the needs of the “dual mode” user is a non-trivial issue. In the Techaisle survey, both small and midmarket firms report that users access a combination of business and personal resources via their business-connected (both corporate-owned and BYOD) mobile devices. This reinforces the importance of some of the solutions being currently used or planning to be used by SMBs. These are solutions that help manage mobile devices that deliver access to corporate information without downloading data and applications themselves (such as thin clients and Windows-as-a-Service) and methods of securing data when it is exchanged between mobile devices and external users and where users themselves move seamlessly between corporate and personal usage modes on devices that are connected to corporate networks.
Mobile devices are an essential component of mobility but mobility itself extends beyond hardware to applications, solutions and work habits. Techaisle’s 2015 SMB Mobility Adoption Trends research shows that the “dual mode” SMB user represents a specific problem for SMB IT staff and the challenges of supporting a mobile workforce go well beyond the device.
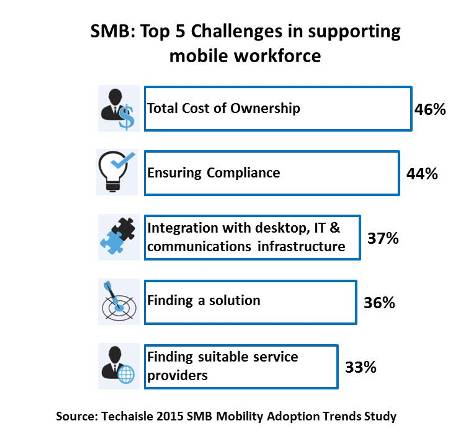
Small and midsized businesses have different challenges in supporting the mobile workforce
Looking first at the small businesses, we see that managing TCO – which includes, in addition to typical IT expenses, service charges that are unique to mobile devices – is rated as the most significant challenge by small business respondents. These firms also struggle with the “on ramps” to mobility: finding appropriate suppliers and solutions and integrating multiple screens are also ranked in the top five challenges encountered by 1-99 employee firms in support of the mobile workforce.
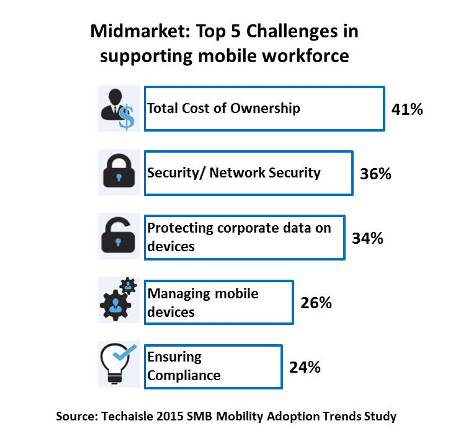
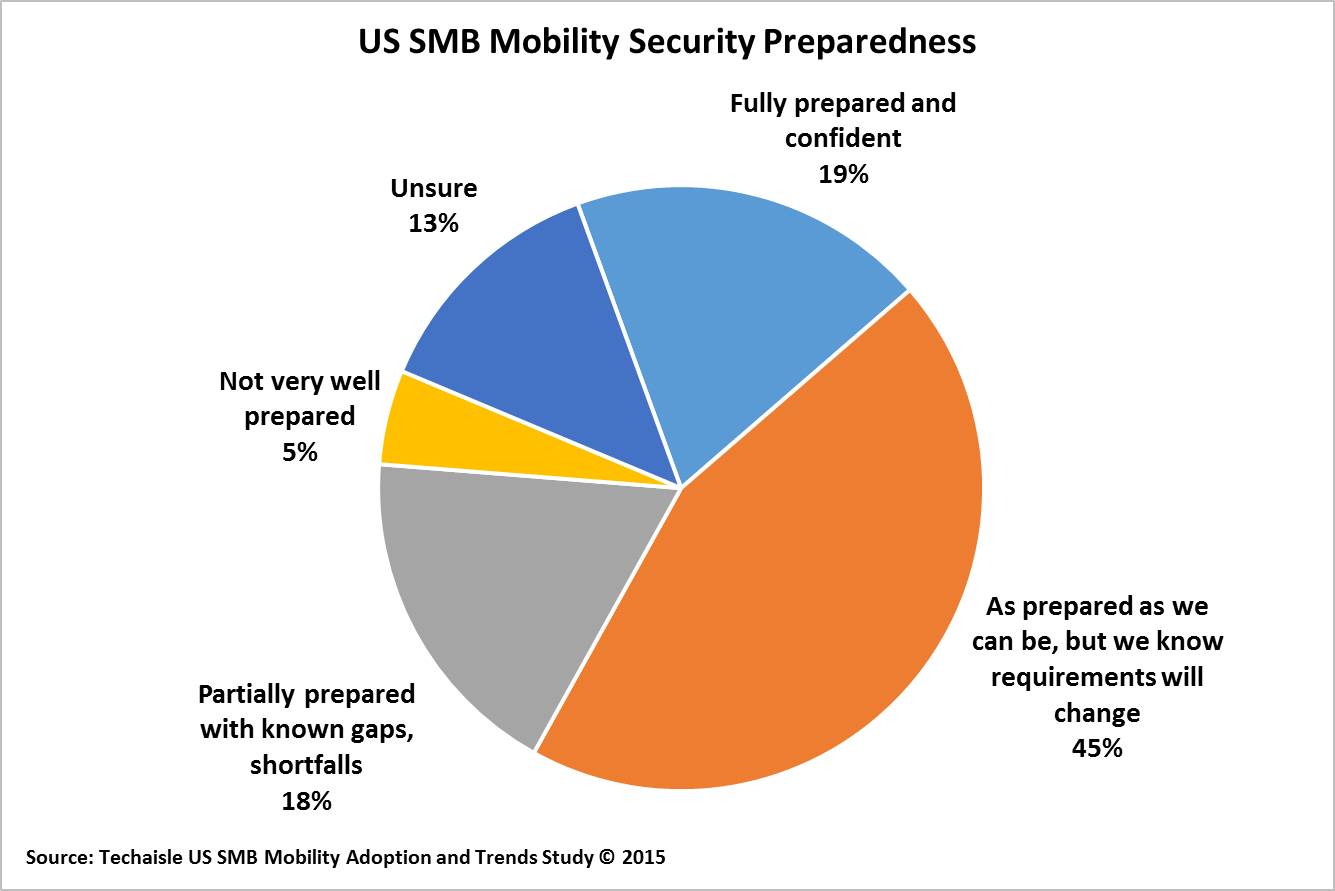
Midmarket firms also count TCO as their most significant challenge. Rather than struggling with mobility on ramps, though, midmarket firms are more concerned with security/data protection and mobile management. Network security, protecting corporate data on mobile devices and managing these devices are all top-five mobility challenges for midmarket IT – and further evidence of why mobility solutions addressing these issues are essential to this community.